Last week, we introduced our customers to the following new content and features within our Security Education Platform, the SaaS-based learning management system that allows organizations to efficiently plan, execute, and measure their security awareness training programs. If you have any questions about these or any of our other solutions, please contact wst-support@proofpoint.com, your Account Executive, or your Customer Engagement Manager.
New and Refreshed Interactive Training
‘Preventing Compromise’ Series
This new two-module series focuses on account and device compromise, as well as attacks like email fraud/business email compromise (BEC). End users learn ways to identify and mitigate the risks associated with a compromised account or device—important skills as organizations continue to face credential-based phishing emails, wire-transfer fraud, and other attacks that attempt to establish a foothold within devices and systems.
Learn more about topics covered in our “Preventing Compromise” training and try a demo version of the module.
‘Workplace Security in Action’
This new scenario-based module reinforces key components of office security by presenting situations end users commonly encounter in daily job functions. Employees practice decision-making related to topics like social engineering, insider threats, and shoulder surfing, ultimately learning to be more attentive to the actions happening around them and how their behaviors can improve workplace security.
Learn more about our “Workplace Security” training and try a demo version of the module.
‘Physical Security’
We have refreshed the content in our ‘Physical Security” module, which focuses on preventing and correcting physical security breaches, and teaches best practices designed to help keep areas and assets more secure. It also helps employees understand the link between physical security and cybersecurity, and how their actions can influence overall cybersecurity postures.
In addition to updated content, the module is now mobile responsive, which allows users to access training on smartphones and tablets as well as desktop and laptop PCs. The ‘Physical Security’ module also now conforms to the U.S. Section 508 standard and the international Web Content Accessibility Guidelines (WCAG) 2.0 AA standard.
Learn more about our “Physical Security” training and try a demo version of the module.
Addition of Greek and Slovak Security Awareness Training Content
We are now translating and localizing training modules, CyberStrength® assessment questions, the End-User interface, and PhishAlarm® response messages into Greek and Slovak. This further enhances our multinational capabilities, which enable organizations to deliver consistent, regionalized security awareness training programs in more than 35 languages.
New Predefined CyberStrength Phishing Assessment
Our Predefined CyberStrength assessments allow organizations to utilize a curated selection of questions to evaluate end-user cybersecurity knowledge and, if desired, automatically assign follow-up training to employees who do not meet or exceed the admin-defined performance threshold.
Our new “Securing Your Email Fundamentals” predefined phishing assessment enables organizations to gauge users’ understanding of the three primary types of phishing lures: dangerous links; malicious attachments; and data entry requests (where email recipients are asked to submit confidential data like login credentials). Administrators can use our Auto-Enrollment feature to automatically assign one or more of the training modules from our “Securing Your Email – Fundamental” series to end users who exhibit a need for additional instruction.
CyberStrength Business Intelligence
Our new CyberStrength Performance Report provides executive-level key performance indicators (KPIs) as well as granular detail that enables organizations to optimize their CyberStrength initiatives. Program administrators can quickly and easily track progress and performance, benchmark results against all available industries, and identify risk from the company level down to the user level.
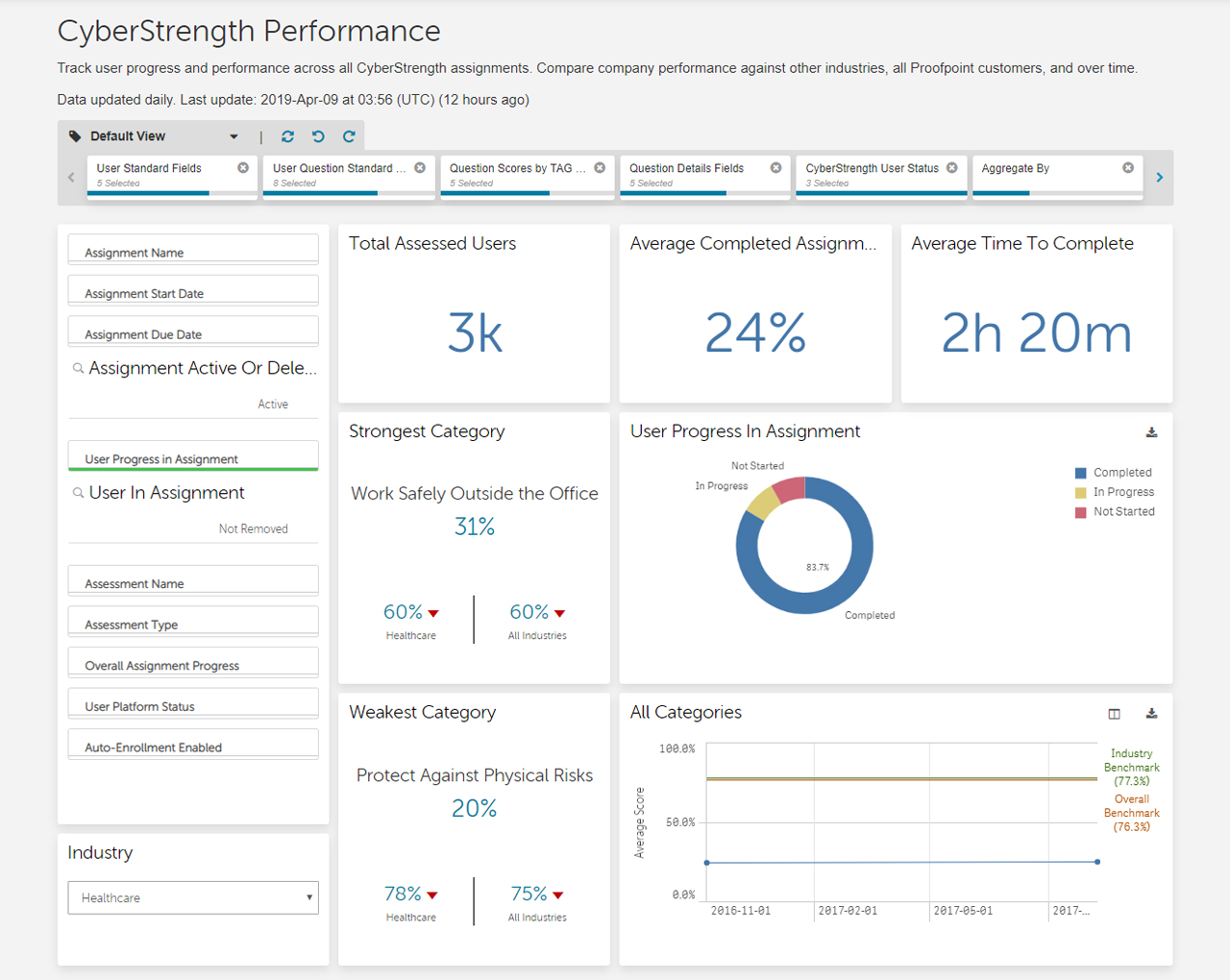
We are also pleased to introduce the CyberStrength Leaderboard, which is available via a tab within the CyberStrength Performance Report. The Leaderboard provides a ranking of best-performing users, a data source that is particularly helpful for organizations that recognize and/or reward employees who exhibit positive cybersecurity behaviors.
Saved Views within Reports
Administrators can now create saved views within our CyberStrength Performance, Assignment User Details, and User Failure Summary reports. Multiple sets of filters can be bookmarked within each of these reports and, as administrators change filters, they can use new features to step back (undo), step forward (redo), and reset the view.
Learn more about our full range of business intelligence features, which enable fast, responsive reporting for your security awareness training program.
Try Proofpoint Security Awareness Training and see how we can deliver results for your organization like we have for thousands of customers.











