

Protect against AI‑scaled attacks across email and beyond
Secure trusted interactions across multiple channels and stages with a single strategic partner
Watch now Explainer Video
As organizations enter the agentic era, attack surface further expands
Threat actors are using AI to take full advantage of how humans work—exploiting trust across employees, business partners, and AI systems themselves.
Modern attacks are AI-driven, multichannel, and multistage, linking email, collaboration and messaging tools, social media, cloud apps, and now AI agents to target people at scale. New AI-specific exploits, including weaponized messages and malicious prompts, further increase risk.
Fragmented security slows response times, siloes teams, and increases cost, leaving critical gaps across collaboration channels—exactly where attackers are accelerating.
Collaboration Security Prime — secure trusted interactions in the agentic workspace
Proofpoint Collaboration Security Prime is our premium solution for protecting trusted interactions and stopping AI-scaled attacks across multiple channels and stages. Built on our industry-leading email security, Prime extends protection beyond email to messaging and collaboration tools, cloud applications, and the supply chain—all through a single, integrated platform.
Prime embeds human resilience directly into the platform, turning real attacks into instant training and simulations. By correlating security events across multiple control points throughout an attack campaign, it accelerates threat response, streamlines operations, and unifies siloed teams.
Key features and capabilities include:
Multichannel defense with Nexus AI
Protects organizations’ employees across email, messaging, browsers, collaboration tools, social media platforms, cloud apps and file-sharing services. Nexus AI applies consistent threat detection across all digital channels to eliminate blind spots, ensuring full-surface protection.
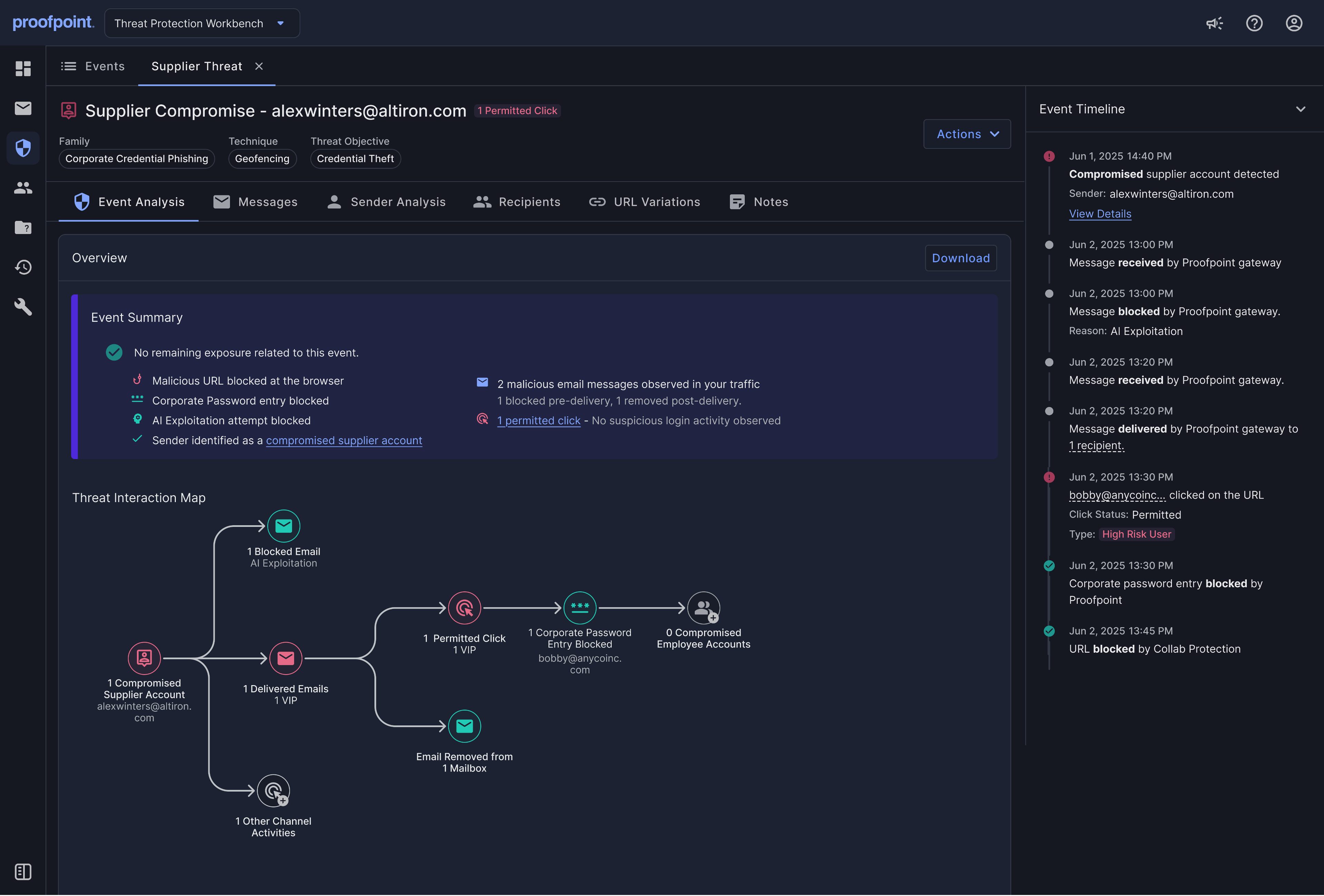
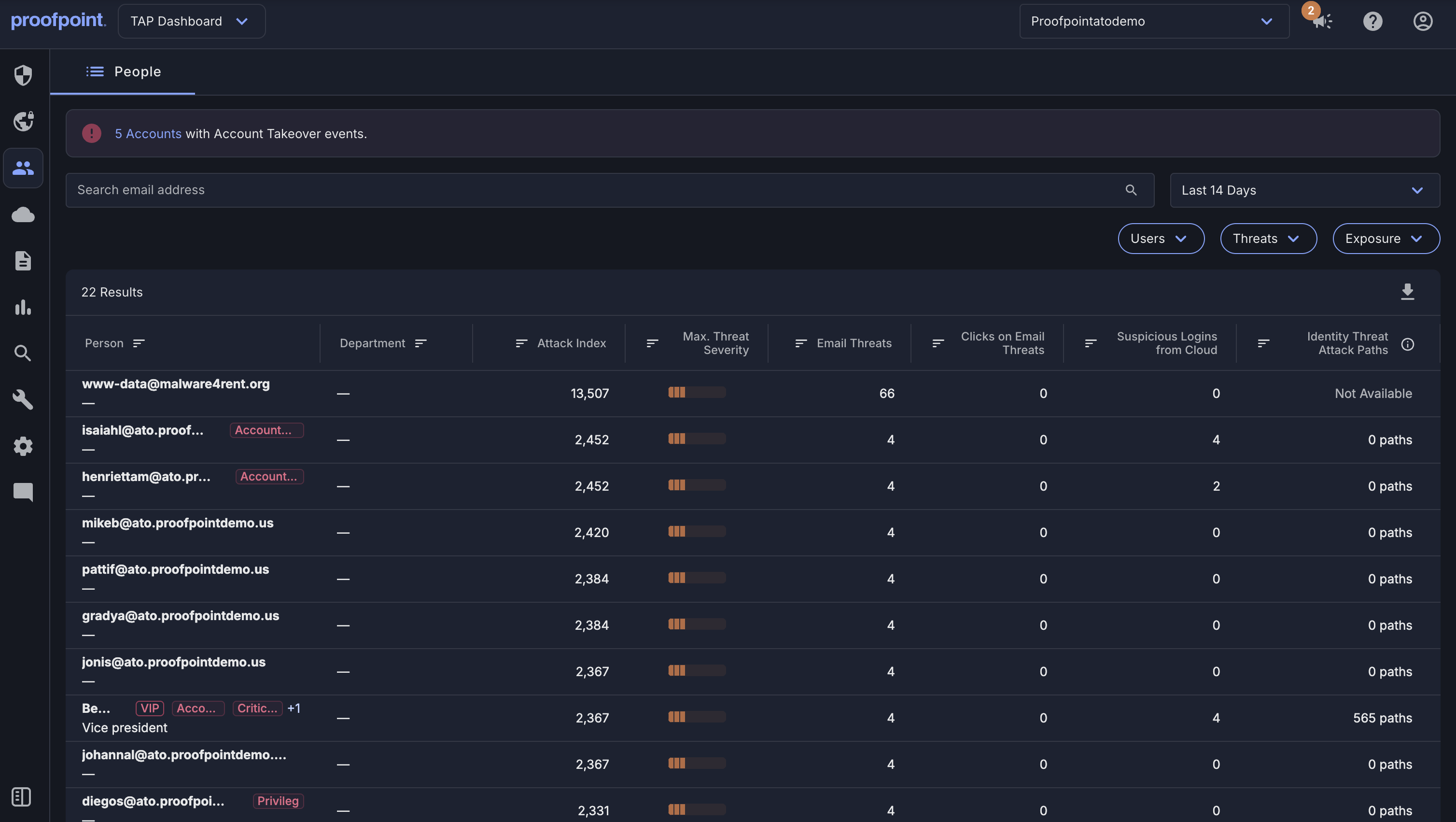
Multistage attack protection
Identifies and remediates account takeovers, lateral movement and supply chain attacks through a unified detection and response workflow. Provides full visibility and ability to investigate and act faster.
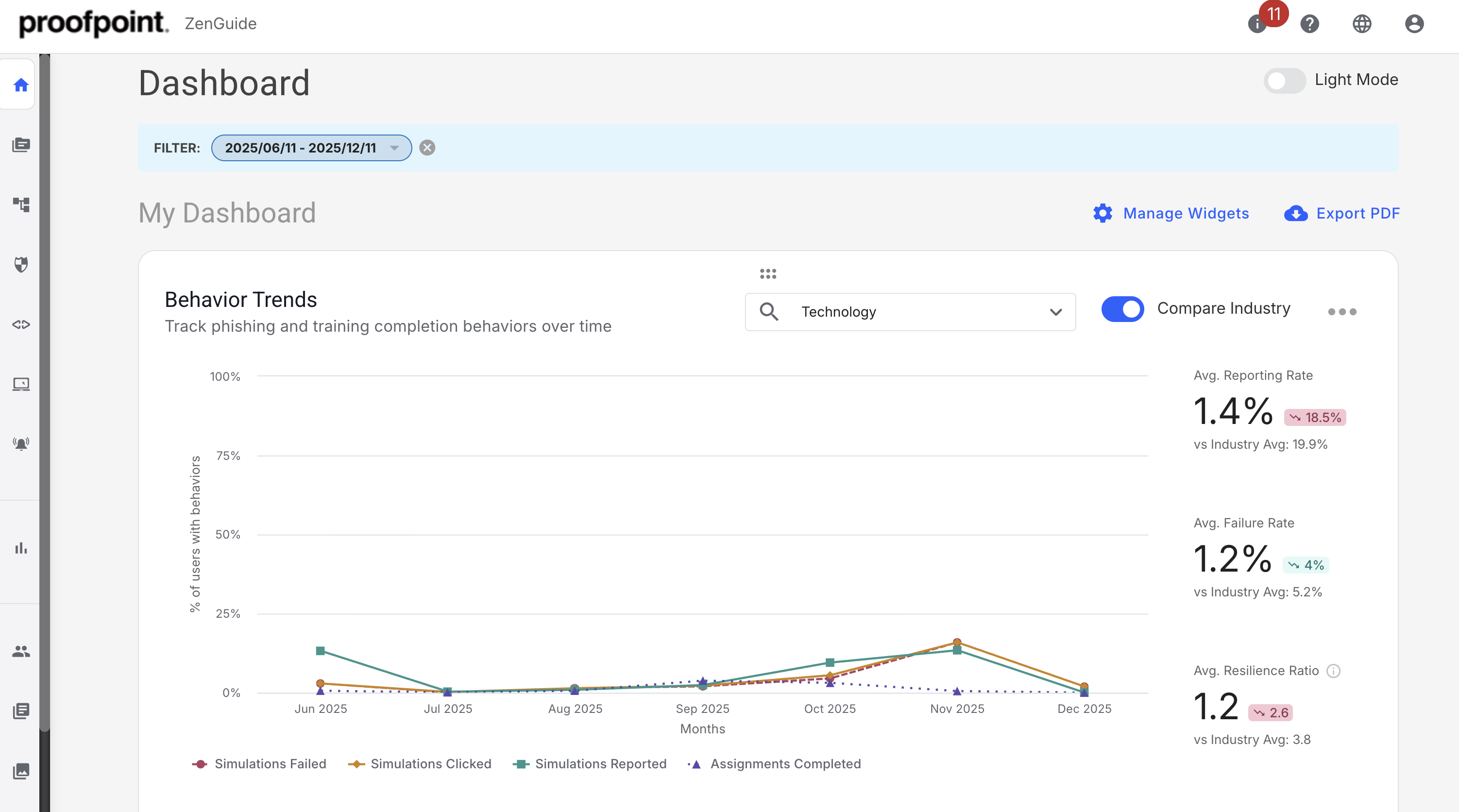
Human risk-based guidance and insights
Identifies at-risk employees and obtain AI-driven risk insights based on user behavior and threat activity. Provides employees real-time, risk-based guidance and targeted education tailored to their attack exposure, behavior and roles. Enables security teams to apply adaptive security controls and coach at-risk employees.
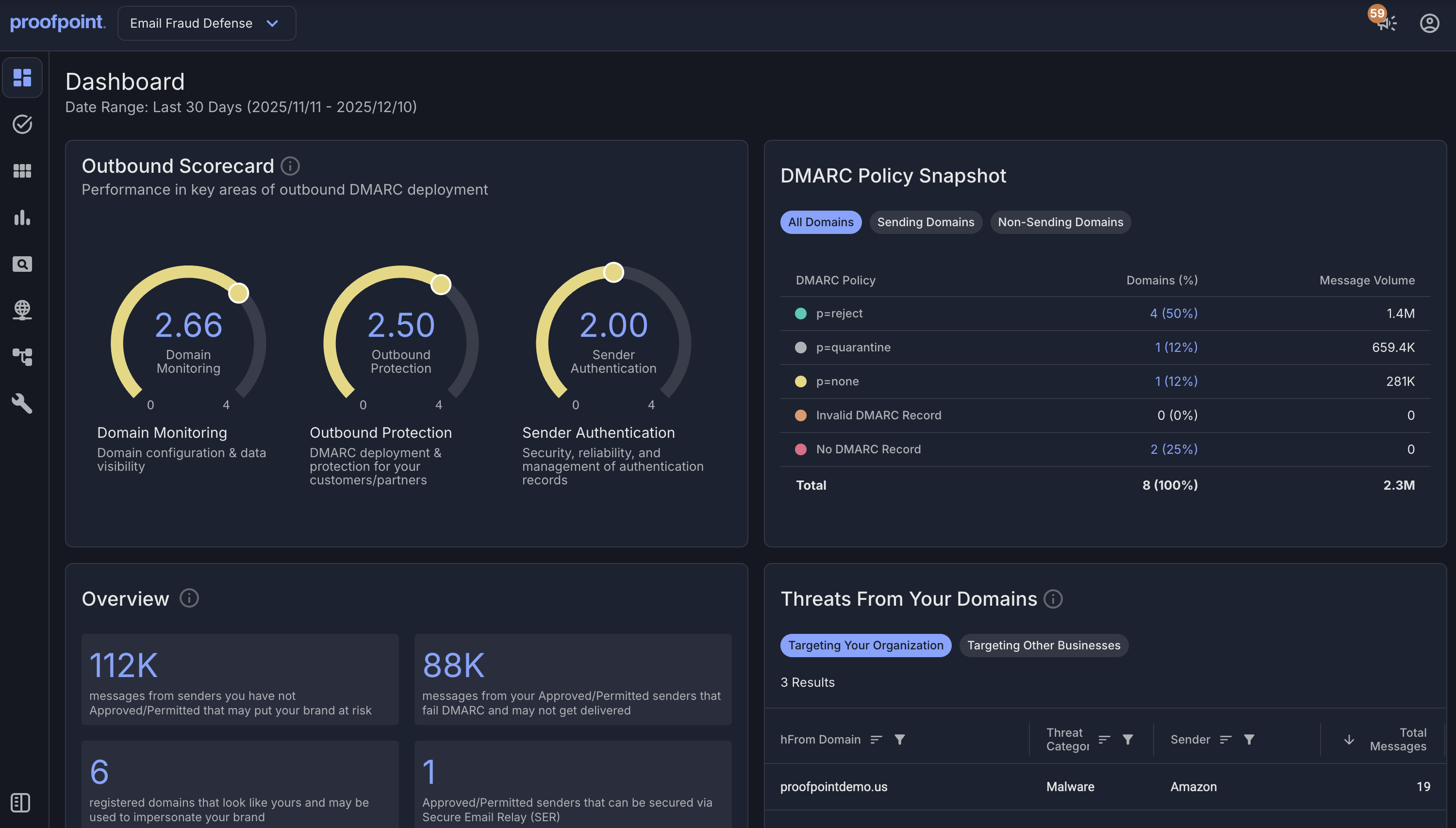
Impersonation protection
Protects trusted domains from various impersonation tactics, such as domain spoofing and malicious lookalikes, using an integrated system that combines email authentication, dynamic discovery of malicious lookalike domains, and takedown services.
Experience the benefits of
Collaboration Security Prime

on average in reduced risk exposure
Achieve completeness of risk reduction
Unlike others that only detect a limited range of threats, Collaboration Security Prime delivers comprehensive protection, preventing the widest array of threats with unrivaled detection accuracy. It blocks threats delivered through various channels, strengthens user resilience and defends against both compromised user and supplier accounts. And it safeguards your trusted business communications while providing deep insights into human risk—ensuring complete security like no one else.

improvement in workforce efficiency
Simplify operations for maximum efficiency
Collaboration Security Prime streamlines security operations by minimizing triage-worthy alerts with industry-leading 99.99% detection accuracy. It reduces labor costs and mitigates the impact of threats through automated workflows and threat response capabilities—improving workforce efficiencies by as much as 75%.

saved by optimizing IT
Achieve more with less through consolidation
With preconfigured integrations across the Proofpoint ecosystem, Proofpoint Collaboration Security eliminates the complexity and overhead of managing fragmented point solutions. You can maximize licensing benefits and unlock access to advanced capabilities at a significantly better value by consolidating vendors and choosing Proofpoint as your single strategic partner.
See the latest Proofpoint Collaboration Security Prime innovations
Proofpoint is a complete solution that gives us full visibility into what’s going on in the communication stack, the people stack and the behavioral stack.
— The Ariston Group
We only need to log into Proofpoint platform on a weekly basis because we can count on it to do its job.
— Linkforce
Proofpoint remains the ideal partner to help us meet the challenges of cybersecurity in an increasingly complex landscape.
— Saipem
Request a demo
Learn how our integrated platform helps you:
-
Stop cyberattacks
-
Prevent data loss
-
Reduce human risk across your environment












