VPNs were introduced nearly 20 years ago to provide secure access between remote employees and headquarters. Two years ago, it was estimated that around the world, 70% of employees were working off-site at least once a week according to Zug, a Switzerland-based office provider.
A Growing Remote Workforce
Over the last five years, and even more so since the beginning of 2020 when Covid-19 began spreading across the globe, there has been an explosion in the need for flexible and secure ways for employees to work from outside the office.
Working from home is no longer a short-term patchwork solution, but a long-term plan. Kate Lister, president of Global Workplace Analytics, expects that for the next two years, up to 30 million employees in the US will need to regularly work from home—up from the estimated five million who do so at least half-time now.
VPNs no Longer Meet the Challenges of Today’s Remote Workforce
VPN’s were never designed to address today’s complex networks, growing user volumes, and high-risk remote access scenarios. With so many users working from insecure locations and unmanaged devices, providing broad network access is a tremendous risk. Another consideration is user experience. The VPN tends to be slow and cumbersome – it's an open secret that users hate their VPNs. Hosted in the datacenter or in a single cloud region, VPNs generally introduce latency as well as complexity. As a result, security and network administrators are realizing that it's more critical than ever to find a robust and secure solution for remote access.
In the Cloud, Remote Security Can be Distributed as Your Workforce
Just as other apps and services have moved to the cloud, security is also finding its way there. Cloud-based security solutions provides a simpler and more reliable approach than traditional on-premises VPN solutions. With many areas recently issuing stay-at-home orders, appliances like VPNs became even more cumbersome due to disrupted supply chains and an increased number of physical locations requiring a visit from qualified technicians. Cloud-delivered products remove the physical obstacles and shift the work and responsibility of updating software back to the vendors themselves. Security solutions delivered via a distributed network of global points of presence reduce latency significantly, which is increasingly critical for a global workforce.
Zero-Trust Network Access for a Secure Perimeter
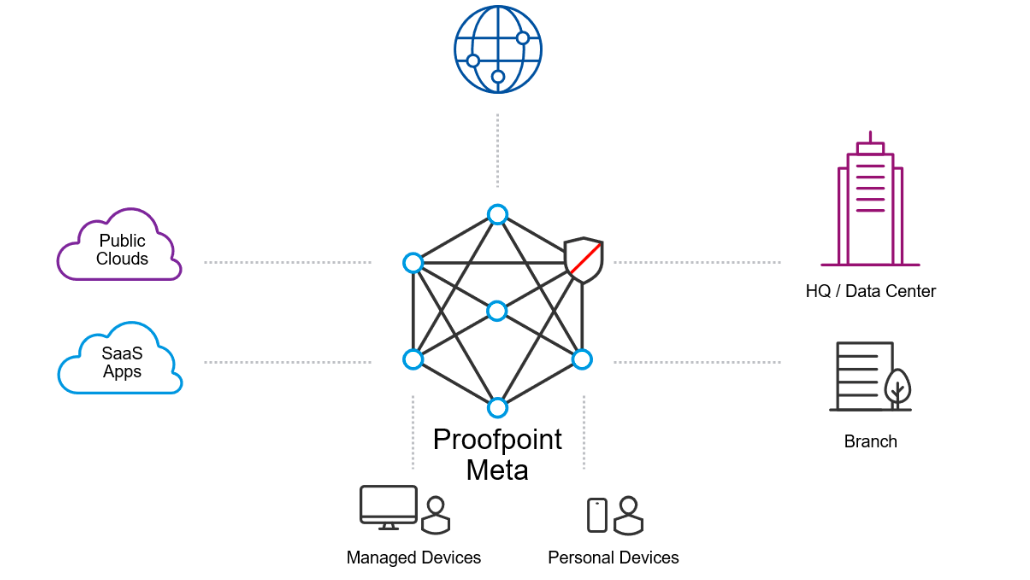
As we head into a new decade, we see the enterprise VPN giving way to the cloud and a new generation of Zero-Trust Network Access (ZTNA) solutions. The ZTNA approach essentially redefines the perimeter to the user and away from the traditional, physical office and datacenter. Unlike traditional gateway appliances, ZTNA solutions are seamlessly deployed and managed from the cloud, enabling quick setup for companies in need of a solution today – not three months from now. The security policy moves to the user’s device, following it wherever it goes, and creating a software-defined perimeter.
Why ZTNA for Today’s Enterprise?
ZTNA enables customized access so each user can access exactly the applications they need, rather than the entire network, offering a huge security advantage over on-premises VPNs. With ZTNA, IT can easily create many granular security policies that associate specific employees or contractors with only the applications and services that they need to complete their work. In turn, every user device receives a unique identity that is continuously verified and authorized in real time. This means that anything they don’t need remains invisible, thus reducing the surface for potential attacks.
In addition, ZTNA provides a virtual air gap between the Internet and internal resources which minimizes the open ports exposed to the internet and prone to attack.
The Rise of Zero-Trust in an Age of Uncertainty
The landscape of network security is changing as more of the workforce stays home. More and more enterprises are beginning to understand the widening gap left by traditional on-premises solutions, and the need for zero trust security will continue to grow as more applications, data, and workloads move to the cloud. Compared to solutions like a corporate VPN, ZTNA is the better choice, offering micro-segmented application access to isolate the enterprise network from threats and prevent data loss. ZTNA offers a comprehensive, people-centric, software-defined perimeter so enterprises can protect their users and their data no matter where they are.
Learn More
Protecting your employees at home is more important than ever. Here’s a list of helpful resources to help you do it. To learn more about how Proofpoint can secure your remote workforce, click here.










