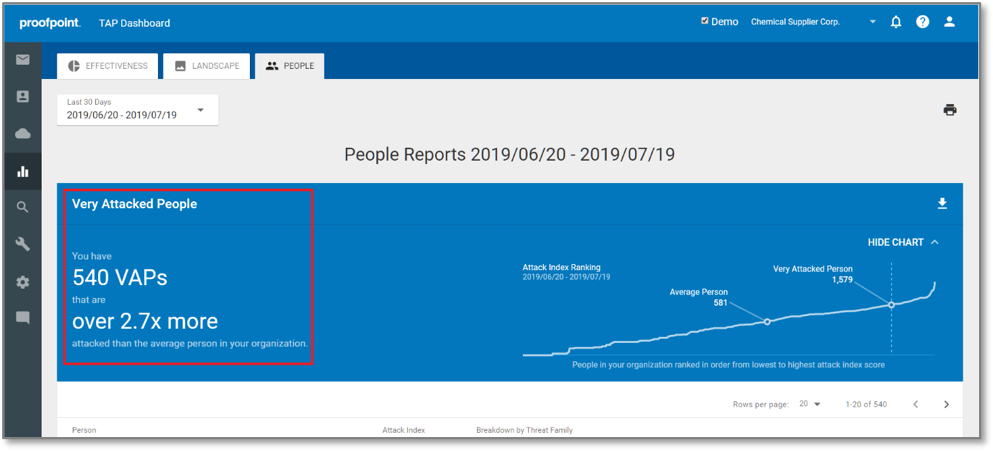
Organizations continue to struggle with attacks developed by sophisticated threats actors trying to infiltrate and steal data. These attacks are more focused on the people than the infrastructure itself. Unfortunately, the people within organizations aren’t fully equipped to handle these types of threats. From our latest Beyond the Phish report, we see that 25% of organizations’ users were unable to answer phishing-related questions. In addition, nearly 20% of users struggled with questions relating to safe internet usage. Threat actors understand your users’ lack of security knowledge and will exploit it in their attempts to attack your organization. In Targeted Attack Protection, we provide visibility into your Very Attacked People (VAPs) to give you a clearer picture of who the attackers are targeting.
To learn more about how we find your VAPs considering reading these blogs:
Proofpoint Launches the Attack Index to Help Companies Better Protect their Very Attacked People
How to Use the Proofpoint Attack Index in the TAP Dashboard, Part 1
How to Use the Proofpoint Attack Index in the TAP Dashboard, Part 2
Getting visibility into your organization’s most attacked people is just one part of the battle, however, you still need ways to prevent the threats from impacting them—and by extension, your organization as a whole. While your VAPs might be the user group most at risk for sophisticated threats, that doesn’t mean they are the only user population that could come under attack. To help provide enhanced security for all users requires not only a multi-layered approach to security, but one that can adapt to the particular risk factors of users and the URLs they click on. That is why we’ve introduced an industry-first, people-centric approach to isolating URL clicks within corporate email. This risk-based, adaptive security control for corporate email systems provides our customers with another layer of security to help prevent threats from spreading within their organizations. This functionality is part of our newly released Proofpoint Email Isolation and Proofpoint Browser Isolation solutions.
So how does this new capability work? Once we have determined who in your organization is most at risk for attack—your VAPs—we can provide a deeper level of security for those users. Whenever they click on any link in their inbox that has been re-written, those URL clicks can be sent to a secure, isolated browser session to prevent any potential threat from impacting the user’s device and spreading to the corporate environment. We want to ensure that all your VAPs’ URL clicks are isolated, because they constitute the user population most at risk from extremely sophisticated attacks reaching their inbox.
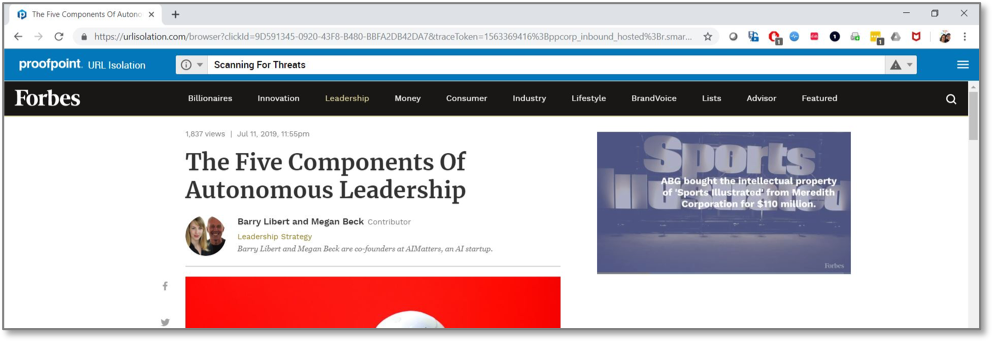
At the same time, for the rest of your users, we can send the riskiest URL clicks (based on various threat intel) to an isolated browser session. When users are in these isolated sessions, they can use the page as usual, but no malicious content will be able to escape the session. After we run the site through deep sandboxing and determine that it’s safe, we can provide an option to allow the users to exit isolation and fully interact with the page—download/upload files, enter information in forms, etc.
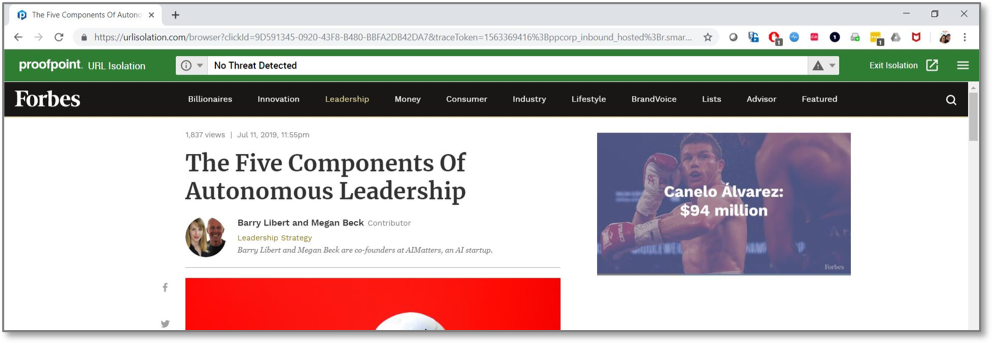
To further reduce the attack surface within your organization, Proofpoint Email Isolation allows you to isolate users browsing personal webmail. This prevents any threats in their personal webmail from impacting the corporate device. In addition, it provides added confidentiality while in personal webmail, because nothing within the isolated session is viewable except by the users themselves. Proofpoint Browser Isolation lets organizations allow users to visit a wide range of what may be considered higher-risk or low-value sites. It isolates these browser sessions to prevent any threats from these sites having an impact on devices or the organization. Instead of your IT or security teams needing to choose whether block various sites, Proofpoint Email and Browser Isolation provides an alternative that gives users the freedom to visit sites, while maintaining the security of your organization.
To learn more about the value Proofpoint Email Isolation and Proofpoint Browser Isolation can provide your organization, please download the report Osterman Research: Why You Should Seriously Consider Web Isolation Technology.










