Key takeaways
- Proofpoint threat research shows that 99% of organizations experienced account takeover (ATO) threats during the study period.
- Targeted attacks win; spear phishing succeeds two times more often than brute-force attacks.
- Post-compromise is the danger zone. 88% of organizations experience abuse after attackers gain access.
In today’s agentic workspace, user credentials have become attackers’ highest-value targets. Organizations rely on cloud platforms, collaboration tools, browsers, and third-party applications to get work done. When threat actors compromise an account, they can use it to abuse trust, automate malicious activities, and expand attacks across all these channels and more.
This risk is even bigger in environments that use automated workflows and AI-assisted agents. Identities increasingly sit at the center of these environments. So, when an attacker compromises an account, they get access to the agents, integrations, and workflows that operate under that identity. In effect, compromise can extend beyond account access into connected systems tied to that identity.
Proofpoint threat research shows that nearly all organizations experience account takeover (ATO) threats. Attackers favor using targeted techniques that exploit trusted relationships. They aim to get post-takeover access—particularly in cloud and collaboration environments, such as Microsoft (Microsoft 365, Teams) and Google (Google Workspace).
This is why it’s important to have robust, login-focused ATO detection in an agentic workspace. When you protect identity, you also help protect the downstream agents and workflows that depend on it.
Research methodology
Proofpoint has one of the largest and most diverse datasets in all of cybersecurity. Between November 2024 and November 2025, Proofpoint reviewed cloud-based account takeover activity across our global customer base of 50M+ accounts.
The dataset included:
- Attempted and successful ATO activity
- Targeted and non-targeted attack techniques
- Post-takeover behaviors across email, cloud storage, collaboration platforms, identity systems, and OAuth applications
The findings below reflect the results from this analysis period.
Top 3 findings
1: Account takeover threats are pervasive
99% of organizations were targeted by ATO threats over the past 12 months, and 67% were successfully compromised. This makes them one of the most consistent entry points for attackers.
2: Precision attacks drive impact
Targeted attacks, such as spear phishing, succeed more than twice as often as those that are non-targeted (66% vs. 29%). This reflects a shift. Attackers aren’t using broad, probabilistic attack techniques as frequently as precision attacks that leverage user context and relationships.
3: Post-compromise abuse is the dominant risk phase
88% of organizations that are impacted by ATO attacks show post-access activity. Threat actors use compromised identities for establishing persistence, fraud, and data theft.
Why credentials and identity dominate the agentic workspace
Modern work no longer happens in a single system. Users, AI agents, and automated workflows depend on identities operating across:
- Cloud productivity platforms, such as Microsoft 365 or Google Workspace
- Email and collaboration tools
- Identity providers and SSO
- OAuth-connected third-party and AI-enabled applications
In these environments, credentials are more than just an access; they are a trust anchor. Once an attacker steals an identity, they can use it to operate as a legitimate user. They don’t need malware to scale their impact quickly and quietly. Instead, they use native features and automation.
Account takeover is a lifecycle, not a login failure
Modern ATO attacks unfold across three interconnected phases: pre-takeover, takeover, and post-takeover. Each phase introduces distinct risks.

Figure 1. ATO Attack lifecycle.
Pre-takeover: targeting trust, users, and suppliers
The pre-takeover phase is where attackers make their most important strategic decisions. They decide who to target, how to approach them, and where to deliver the initial attack.
Proofpoint research shows that while 98% of organizations are targeted by both non-targeted and targeted attacks, the likelihood of success diverges sharply once attacks are delivered.
What Proofpoint observed:
- Non-targeted attacks (such as broad phishing or password spraying) resulted in a successful compromise in 29% of organizations
- Targeted attacks (designed around specific users or trusted relationships) resulted in successful compromise in 66% of organizations
This disparity explains why attackers increasingly favor targeted approaches. Rather than relying on scale alone, attackers invest in precision and context. They often use compromised suppliers or trusted external partners to initiate attacks, which appear legitimate and align with real business activity.
Messages that reference active projects, existing relationships, or shared documents blend naturally into day-to-day workflows—especially in cloud and collaboration environments. This significantly increases the likelihood that an initial attack leads to an account takeover.
Takeover: when compromise occurs
The takeover phase begins when an attacker successfully gains access to a user account and transitions from attempting entry to operating as that user. This is the point at which account takeover shifts from a security control failure to a business risk event.
What Proofpoint observed:
- 67% of organizations were impacted by one or more ATOs
- Of that group, 59% had MFA enabled on compromised accounts
These findings underscore a critical reality: MFA is necessary, but it’s not enough. As MFA adoption has increased, attackers have adapted. Techniques such as session hijacking, adversary-in-the-middle phishing, and OAuth abuse enable them to gain access without defeating authentication outright. As a result, successful ATOs increasingly occur even when MFA is in place.
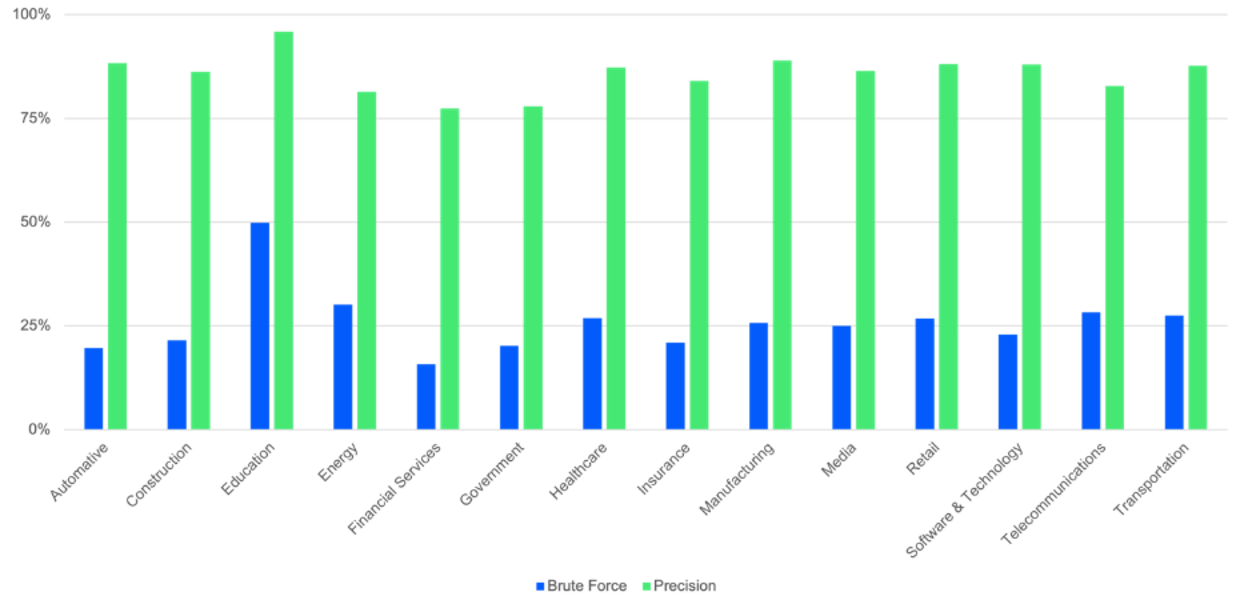
Figure 2. Breakdown of industries that experienced a successful ATO attack, comparing non-targeted attacks vs. targeted attacks.
Proofpoint researchers also observed meaningful differences across industries once attacks reached the takeover phase.
What Proofpoint observed:
- Financial services organizations had the lowest percentage of impacted tenants.
- Education organizations had the highest percentage of impacted tenants.
This pattern held true for both targeted and non-targeted attacks.
It’s likely that this contrast reflects differences in operating constraints and security maturity. Financial services organizations typically benefit from sustained cybersecurity investment, stricter regulatory requirements, and more mature identity and access controls. These factors reduce the likelihood that attacks progress to successful takeover.
In contrast, education and broader public sector environments often face tighter budgets, slower adoption of newer security technologies, large and frequently changing user populations, and lower baseline security awareness. All these conditions increase the likelihood that both targeted and non-targeted attacks succeed.
Post-takeover: persistence, abuse, and expansion
The most important insight from Proofpoint’s post-takeover analysis is not simply what attackers do, but it’s how consistently they act. 88% of impacted organizations show post-access activity. Post-access activity varies across different activity types as seen below.
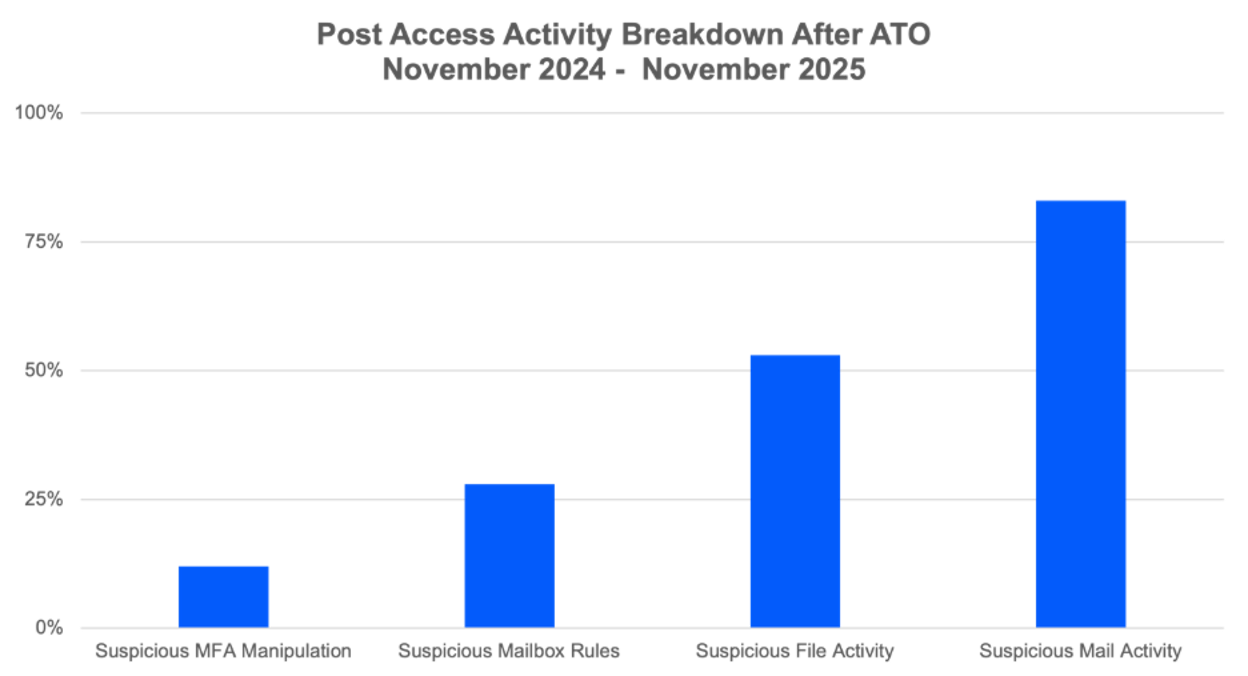
Figure 3. What attackers do after they compromise an account.
- Suspicious MFA manipulation (12% of organizations impacted). Threat actors may manipulate MFA settings on compromised accounts. They might add other MFA factors, downgrade MFA methods, or make other changes to ensure persistent access to compromised accounts.
- Suspicious mailbox rules created (28% impacted). Newly created mailbox rules help the threat actor hide unauthorized activities, delete evidence, steal data, and facilitate fraud.
- Suspicious file activity detected (53% impacted). Threat actors may use compromised access to conduct suspicious file activity. This includes downloading or uploading files, accessing sensitive files, and stealing data.
- Suspicious mailbox activity detected (83% impacted). Threat actors can use compromised mailboxes for follow-on attacks. They might conduct business email compromise (BEC) or exploit existing trusted relationships to target other organizations with phishing attacks.
Most notably, our research shows that 83% of impacted organizations observed suspicious mailbox activity after an account takeover.
With access to a user’s mailbox, attackers can read private messages. What’s more, using AI, attackers can automatically scan multiple messages so that they can learn about user relationships and get a feel for the tone of their messages. They can map relevant attack targets at a fraction of the time it would take manually, and across all languages.
They can also identify trusted contacts both inside and outside the organization. It’s this context that enables them to send highly convincing follow-on attacks that feel legitimate. Messages are grounded in real conversations and real trust.
As a result, account takeover quickly evolves from an identity breach into a violation of personal and professional privacy. It’s a powerful mechanism for impersonation, fraud, and supplier-based attacks.
OAuth and AI-enabled apps amplify post-takeover risk
Post-takeover abuse increasingly includes OAuth application manipulation, particularly as AI-enabled apps proliferate.
Proofpoint research showed:
- Users granted access to 241,954 third-party applications within their environment over the past year.
- Approximately 7,000 new apps were granted consent per month.
- 49 of those consented applications were identified as malicious.
- AI-enabled consented apps grew from 11,290 to 258,033 —an increase of more than 2,100% in under a year.
OAuth abuse allows attackers to persist without credentials, often surviving password resets and MFA enforcement. As AI-enabled applications become more common, attackers can disguise malicious apps as helpful tools, further exploiting user trust.
How Collaboration Security Prime can help
Account takeover is no longer an edge case—it is the backbone of modern cyberattacks in the new agentic workspace.
Organizations that continue to treat ATO as a login problem will struggle to keep pace. Those that adopt a lifecycle-based approach, focused on continuous monitoring and automated response, will be best positioned to reduce risk.
Proofpoint’s Collaboration Security Prime is uniquely built to help address this growing problem. Prime delivers unified visibility and response across email, cloud, collaboration platforms, browsers, and identity.
By correlating signals across the full ATO lifecycle, Prime helps you to:
- Detect targeted attacks earlier, including those that come from compromised suppliers
- Identify and contain takeovers faster, even when MFA is bypassed
- Surface post-takeover abuse, such as mailbox activity that personalizes attacks
- Reduce dwell time by automating containment across channels
Rather than relying on siloed point solutions, Prime delivers end-to-end protection across the trusted interactions attackers abuse most.
To learn more about Proofpoint Collaboration Security Prime, schedule a meeting with a Proofpoint specialist.











